2 min read
eIDAS: Driving Business Through Transparency
eIDAS has brought a breath of fresh air to a darker aspect of the technological sector; it’s taken a subject that is sometimes surrounded by a cloud...

2 min read
eIDAS has brought a breath of fresh air to a darker aspect of the technological sector; it’s taken a subject that is sometimes surrounded by a cloud...
3 min read
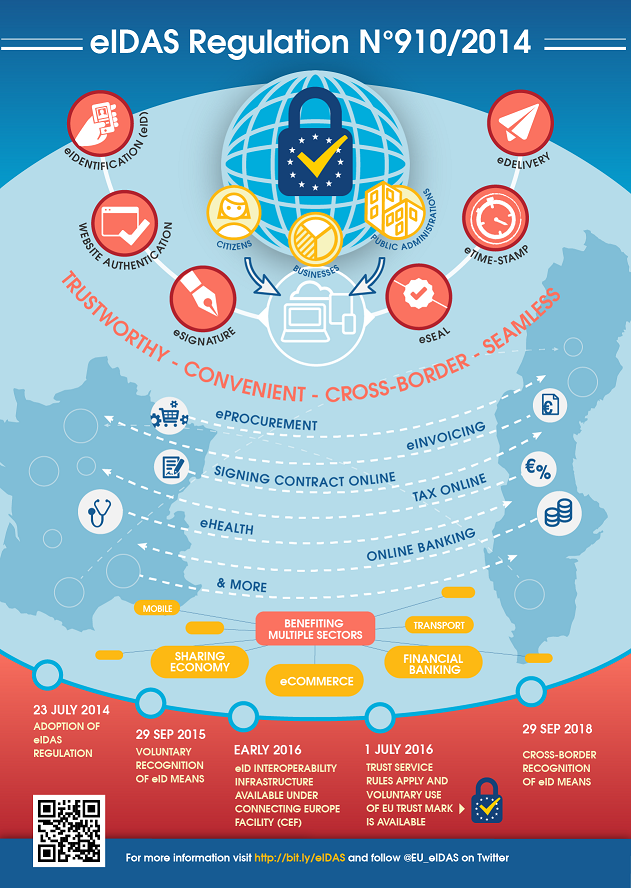
As of 1st July 2016, the first phase of the EU’s new regulation on electronic identification (eIDAS) will become enforceable. But amid all the...
3 min read
When an electronic signature is created, it must be associated to the data that it is being used to secure. This is accomplished by creating a data...

4 min read
On December 19, 2003, ZertES, the Swiss Federal law regarding the use of certification services with electronic signatures was approved into law.

2 min read
Technology is constantly introducing the business world to new tools, processes, and analytics that transform the way people conduct business....

3 min read
This article explains what an electronic signature policy is from the perspective of a CISO or other person required to maintain information security.

4 min read
The term XAdES stands for XML Advanced Electronic Signatures, which specifies a set of extensions that are used with the W3C recommendation for XML...

2 min read
Under the Computer Security Act of 1987, the National Institute of Standards and Technology (NIST) was authorized to approve standards and set...

3 min read
The term CAdES stands for CMS Advanced Electronic Signatures. The Cryptographic Message Syntax (CMS) provides a framework for digitally signed...