4 min read
Manual vs. Automated Key Management
This article evaluates and compares manual and automated cryptographic key management. It looks at security-related issues as well as organizational...

4 min read
This article evaluates and compares manual and automated cryptographic key management. It looks at security-related issues as well as organizational...

4 min read
EMV chips on payment cards contain cryptographic co-processors and dual interfaces that allow for contact and contactless payment options. When...

2 min read
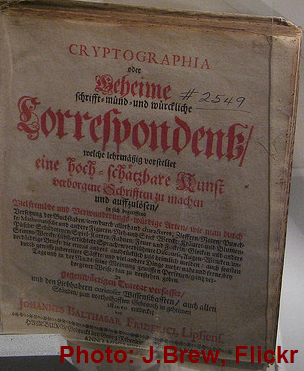
Cryptography is the foundation of protecting electronic data and cyber security. Encryption can effectively prevent breaches while also protecting...
2 min read
This article discusses the importance and usage of documentation for a key management system within an organization.

4 min read
This article discusses the functions and use of hierarchical layers when establishing a cryptographic key management policy, and how the policy...

2 min read
A cryptographic zone exists between two points, where a symmetric key or asymmetric public keys are shared in order to encrypt sensitive information....

10 min read
This article gives an insight into the EMV chip technology, which is being rolled out on a world-wide scale to increase the level of fraud protection...
2 min read
This article introduces and describes the relevant roles needed to successfully manage a key management system in an organisation.

3 min read
The period of time between the key activation and key deactivation is called the crypto period of the key. The crypto period is defined by factors...